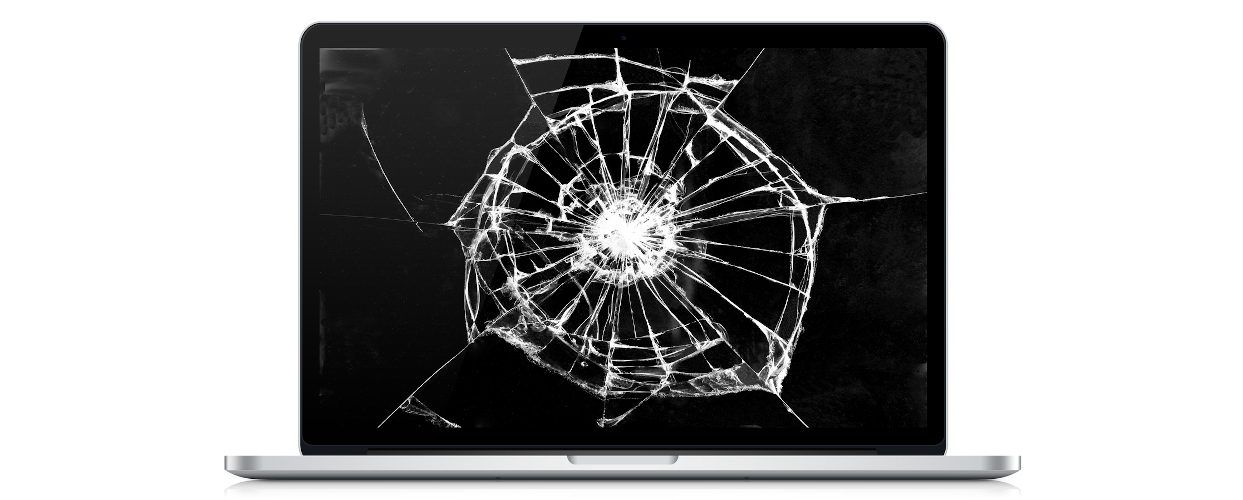
Computer Repair
Call us today and get an estimate or get the repair started today! We'd love to hear from you and fix the problem ASAP!
Great Prices
No one wants to pay a lot for computer repair. You already spent hundreds or thousands on the computer. Now when something's wrong- you don't need to get "soaked" on the fix.
Friendly Techs
At BTS, you're treated with respect and kindness. No one likes being talked down to. Not everyone wants to be a tech support geek when they are growing up. We did, and here we are to help!

Fast Service
You want to get your computer repaired as fast as possible. We make that happen. Most repairs are done within 2 to 3 business days... not weeks like some places.
Are you ready to get that computer repair started?
Click the button on the right to send us an email, or call the number below.
Get In Touch
We would love to hear from you!
p 612.276.2308
e sales@broadviewtech.com